General Explanation
Type: Adware
Degree of destruction: low
Prevalence: average
What is Adware?
Adware is a type of advertising malware that is the reason for displaying multiple advertisements or banners on your system and intrigues you to buy different products using its services. Developers of this kind of malware add related codes to notification services in their applications in order to display advertisements and earn more money. They try to intrigue more users to use their applications by adding them to the android stores.
What is Notifyer?
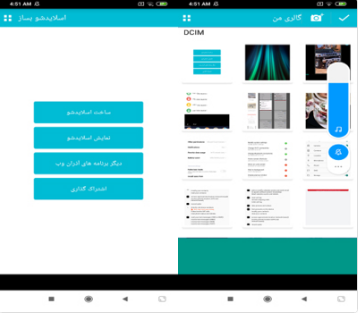
Notifiyer adware show advertising notification in the background to the user using sending notifications services. If the user clicks on each of the notifications the advertisement pages will open in the browser.
Technical Explanation
This malware uses Pushe notification services and an ‘adad’ advertising package to send notifications, and displays targeted advertisements to earn more money; it also displays pages on Telegram and Instagram. The ‘initialize’ method in the main activity of the application is responsible for checking the user’s phone API, and if its value is greater than or equal to 9, then the Pushe package can be executed. Also, the installation of Google Play Services will be checked on the user’s phone, so that it can update and execute the Pushe package.
MyPushListener service
This service is recalled by the ‘co.ronash.pushe.Receive’ action, which means, as soon as it receives the message, the Pushe package will be executed. First, this method with two JSON input parameters will check the length of the JSON input parameter not to be zero and then put the type of the message in an intent. If the ‘intent’ equals to “telegram” string, it will open a page on the Telegram application; if its value equals to “Bazar” string, then it will open the name of the desired application package on Café Bazaar; and if the value equals to “link” string, then it opens the specified link inside the phone browser.
public void onMessageReceived(JSONObject paramJSONObject1, JSONObject paramJSONObject2) {
if (paramJSONObject1.length() != 0) {
Intent intent;
final String link;
Log.d(“Pushe”, “Jsoni Ke Ferestadi Khalie”);
try {
intent = paramJSONObject1.getString(“type”);
if (intent.equals(“telegram”)) {
str = paramJSONObject1.getString(“link”);
(new Handler(getMainLooper())).post(new Runnable() {
public void run() {
Intent intent = new Intent(“android.intent.action.VIEW”, Uri.parse(link));
intent.addFlags(268435456);
MyPushListener.this.startActivity(intent);
}
});
return;
}
} catch (JSONException paramJSONObject1) {
Log.e(“”, “Exception in parsing json”, paramJSONObject1);
return;
}
if (intent.equals(“bazar”)) {
str = paramJSONObject1.getString(“packagename”);
intent = new Intent(“android.intent.action.VIEW”);
intent.setData(Uri.parse(“bazaar://details?id=” + str));
intent.setPackage(“com.farsitel.bazaar”);
intent.addFlags(268435456);
startActivity(intent);
return;
}
if (intent.equals(“link”)) {
Intent intent1 = new Intent(“android.intent.action.VIEW”, Uri.parse(str.getString(“link”)));
intent1.addFlags(268435456);
startActivity(intent1);
return;
}
}
}
Free activity
The general function of this activity is to display notifications for advertising its desired application to the user. First, in its ‘onCreate’ method, the Pushbots library will be initialized. Namely, it recalls the ‘init method that checks the application sdk version (the Pushbots library is executable if the sdk version is higher than 8), application package of the Google Services Framework (this application manages different types of Google Connection services such as Cloud Messaging), and demanded permissions to execute this library (android.permission.INTERNET ،android.permission.ACCESS_NETWORK_STATE, and android.permission.WAKE_LOCK). If mentioned terms are applied, and if the Push service is active, the user’s phone data collect as follows, for being registered inside the Pushbots.
- getUDID method: the value of android_id
- TimeZone.getDefault().getID: Time zone ID
- getNetworkOperatorName: the type of the network operator
- Build.VERSION.RELEASE: version type of the OS
- Build.MODEL: user’s phone model
- getLanguage: local language code using locale.getCountry method (local zone country code)
- getNetworkCountryIso: The ISO code of each country’s network
Then, the onClick method will be executed. In this method, the application address “bazaar://details?id=com.powerapp.goollp” will be opened inside the Café Bazaar market to be installed, and the related page to this application will be viewed as “NASA Virus Detector”

The ‘onClick’ method will be executed for 60 existing buttons in this activity with a similar function, and the only difference is the name of the application packages. The malware directs the user to Café Bazaar to download the following applications for advertisement purposes (currently, none of the following applications exist in the Café Bazaar market, and if you search the name of the application package you will face the message: “This application has been withdrawn from the publish mode upon the developer’s request”.
| No. | Name of the Package |
| 1 | com.andromo.look.appsandromolook |
| 2 | com.starmob.bapp |
| 3 | com.powerapp.goollp |
| 4 | andromo.ewrekokofr.ftuufr.androkokomodataapp |
| 5 | com.dir.coopen.fgf |
| 6 | com.powerapp.full.screen.id |
| 7 | com.powerapp.looka |
| 8 | com.init.app.view.yafoo.sss.aaa.www |
| 9 | com.andromo.games.softch.andrmosoftko |
| 10 | and.AppDetails2016 |
| 11 | himan.androidplas.com.cctv_Dozdkir |
| 12 | ir.mm.app.book |
| 13 | com.ppp.ooo |
| 14 | com.utopia_anti.AntivirusSecurityScanner |
| 15 | com.zavaryanmaggmant.andromoapps |
| 16 | com.secovrfgdfdfqp.andromo |
| 17 | ir.andromoapdsd.andromonaqash |
| 18 | com.utopia.fullscreencallerid |
| 19 | com.gpsutopia.studio.apps.route.finder.map |
| 20 | com.AppDetails.apps.around.me.places.gps |
| 21 | com.AppDetails.iphone6.ringtones |
| 22 | com.ppp.powerapp.app |
| 23 | com.fing.woond.shoond |
| 24 | com.rabin.daood.fatm.tqe.gaa |
| 25 | com.zavaryanmaggmant.andromoapps |
| 26 | com.slovise.voices.lock |
| 27 | com.andromocompanybatreii.andromobatreii |
| 28 | com.and.copanyapp |
| 29 | com.reg.mhr.ede.asa |
| 30 | com.andromo.frtfr.deiwed.sger |
| 31 | andromo.gtrandromointernet.andromoapps |
| 32 | himan.androidplas.com.Mashin_GPS2015 |
| 33 | com.utopia |
| 34 | com.hm.ty |
| 35 | com.andromorwsw.rhdskshn.toqozpangon |
| 36 | ru.utopia.supervisor |
| 37 | com.powerappjj.station_clock_7_mobile |
| 38 | com.powerappddd.clock |
| 39 | analog.fff.stylish |
| 40 | com.popop.analogclock_7mobile |
| 41 | com.powerapp.modern |
| 42 | imagic.powerappgogo |
| 43 | com.andromo.app.app.andro.rew |
| 44 | com.androidpawerapp.livewallpaper |
| 45 | com.andromocompanybatreii.andromobatreii |
| 46 | andromogzx.notehaft.daimashntooapp |
| 47 | com.andromoapiui.wedslooklaserfooktoolook |
| 48 | com.andromo.tedansfdtealphairanceellhcmtree |
| 49 | com.andromo.ewserqwswjutyhflkfaktomood |
| 50 | andromoapps.qwere.mashoin |
| 51 | ir.andromolookssccreen.andromogamseappser |
| 52 | com.gaemeandromo.vf.andromoanppsgamres |
| 53 | com.xandromoapps.mashinhayolaa |
| 54 | com.mn.tray |
Hiee_Apple activity
The other displayed notifications are for “membership registration” applications. If the user clicks on this notification, he/she will direct to the download address of the desired application on Café Bazaar. This notification displays to the user once every two days. Also, by tapping on the “Exit Application” button, the user will view a dialogue to be a member of the “Love Quotes” telegram channel, and if the user clicks on it, the register page to this channel will be open.
How to deal with it and disinfect the system
Install and update the Padvish Antivirus database and scan your device to assure that your device is not infected.
How to prevent your phone from infection:
- Avoid downloading and installing applications from unauthorized resources and mobile markets
- Pay attention to requested permissions when installing mobile applications.
- Continuously back up your stored files and data.
- Do not use an unofficial version of applications. Applications such as Telegram and Instagram have many unofficial versions, and most of them are distributed through Telegram channels.